Small Business Security Essentials - How To Keep Your Sensitive Information Safe
What Is Information Security?
Keeping sensitive documents safe and protected has always been a struggle for business owners, especially since the advent of the Internet. Information security has often been cited as the main reason small business owners are hesitant to incorporate use of the Internet-based, “Cloud” computing into their office’s infrastructure. And since even large corporations that actually have the resources to prevent these kinds of security breaches still struggle to keep their own digital assets secure, it’s easy to see why this belief persists.
How can a small business owner or start-up keep their sensitive documents from being hacked?
ChooseWhat has built a Step-By-Step Guide to Keeping Your Sensitive Information Secure that covers how to perform a security evaluation of your company’s data, steps to remove current security threats, how to prevent future threats and how to properly dispose of sensitive documents.Let’s start with identifying what “sensitive information” is to your company. BusinessDictionary.com describes sensitive information as privileged or proprietary information which, if compromised through alteration, corruption, loss, misuse or unauthorized disclosure, could cause serious harm to the organization owning it. Many stock traders will tell you that a Twitter account is sensitive information after the Dow Industrial Average dropped 143 points in response to a hacked tweet that was sent from the AP Twitter account. Either way, it is very important that you, your company and your clients’ information is kept secure. A security breach could wreak havoc on your bottom line, future customer acquisitions, and/or lead to fraud or identity theft.
Step 1: Evaluate Your Company’s Assets & Identify Sensitive Information
- Start by outlining each room of your office.
- If you work virtually, treat each your digital devices as an “office room” and take inventory of all personal and sensitive information stored or transmitted through these devices.
- When going through each room or device, log each piece of equipment and its purpose.
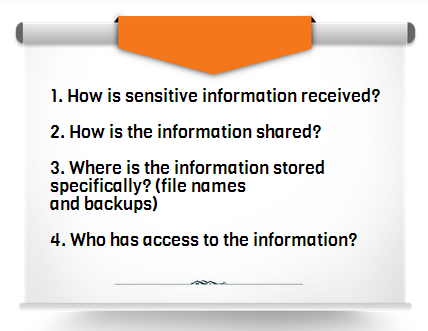
- Answer the following questions for each piece of equipment that deals with sensitive or personal information:
Step 2: Remove Current Security Threats
- Review your equipment log and identify sensitive information you do not need.
- Are you using sensitive information as employee or client identifiers? One of my former employers used my social security digits as my employee username. This is a BIG NO-NO.
- Only use social security numbers, credit card numbers and other financial information when dealing with tax documents or processing payment.
- Never ask for this information if you do not need it.
- If you do need to acquire this information, wait until the last possible step to request this information, especially online.
- There are many ways that your website and digital assets can be hacked without you ever realizing it.
- Dispose of any sensitive information after you use it properly.
- When processing payment with a credit or debit card, never include the expiration date and/or more than 5 digits on the sales receipt.
- Also, ensure that you are using a Secure Sockets Layer (SSL) for all online transactions and sharing of financial and personal data. Intuit has great options for handling secure online shopping and payroll.
Step 3: Preventing Security Breaches
Addressing Digital Security
- Take inventory of any new IT equipment that collects sensitive information. Include the VIN number so you can check these periodically to ensure they have not been switched.
- Identify all connections to the computers and electronic equipment that may contain sensitive data.
- iPhone’s, Dropbox accounts, online fax storage, digital copiers, etc.
“According to the Federal Trade Commission (FTC), the nation’s consumer protection agency, your information security plans also should cover the digital copiers your company uses. If the data on your copiers gets into the wrong hands, it could lead to fraud and identity theft.”
- Get rid of your traditional fax machine and switch to an online faxing service.
- Faxing is the only legal way to transmit sensitive documents besides a physical hand-off. Although, traditional fax machines store faxes in a hard drive that is accessible without a password and easily hacked.
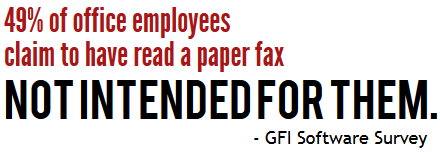
- Also, paper documents are sent to a physical location where faxes can be viewed by anyone who passes by the fax machine.
- Use a password management service like Last Pass or Dashlane.
- Inc.com has outlined four additional services and their costs and benefits here: Review: Password Management Tools
“How many times have you heard of high-security passwords being stored on post-it notes or slips of paper in desk drawers? The simple fact is that good, secure passwords are not easy to remember. If you want to have a secure environment, you have to make password access secure and easy. That requires elegant password management,” says David Chang of FindAFax.com.
- Do not store sensitive information on electronic devices that are easily stolen or lost, like laptops and smartphones. If information is stored on these devices, the files should be encrypted and an “auto-destroy” feature can be added to your hard drive. We recommend using a secure online backup option, like iDrive Online Backup, although Aegis has a couple of great external hard drive options with this incredibly useful “auto destroy” feature:
- Regularly run anti-virus and anti-spyware on all of your computers
Addressing Physical Security
- If your company handles a lot of sensitive information, it is important that you address your physical security as well. While each office or storage location may be different, as a business owner you should clearly define your employee guidelines, responsibilities, and restrictions in regards handling sensitive information. It is important that you and your employees know how to prevent security breaches BEFORE they happen.
- Make sure your employees log-off their computers and lock all cabinet doors prior to leaving each day.
- If you file sensitive information in room where many people come and go, lock all files and start a “sign in/out” system so you can keep track of who is accessing the files. This is also important if you keep data in an off-site storage facility.
Step 4: Disposing of Sensitive Information

- As I mentioned before, it is important that you dispose of any sensitive information you no longer need. Here we will address how to safely get rid of this information without having to worry about security issues.
- Make shredders available throughout your office, especially around copy machines, fax machines and mail areas. Employees should be instructed to shred the sensitive documents immediately after use.
- Do not create a “To Be Shredded” box or file; this will only increase the chances of a security breach.
- Electronic devices should be erased completely before being disposed. White Canyon Software has some great options for this type of action.
- WipeDrive Small Business – to completely wipe electronics before disposal
- WipeDrive SecureClean – to schedule automatic cleanings of “deleted” files, cached, browsing, online banking info, etc.
These are just the basic steps to preventing a security breach and should be adjusted based on your industry requirements and payment processing needs.
In recent years “hackers have elevated their standards,” explains David Chang. “And while breaking into your computer is nice, breaking into your server is that much sweeter -- with much more bandwidth, storage, visibility, and potentially valuable content. Hacking has also gone from a black art to an easy diversion, practiced by thousands of miscreants and aided by publicly-available tools and utilities. You should be ready for a security breach, just like any other disaster that might befall your business.”
Your Feedback Helps!
Add your own recommendations in the comments below or head over to our forums to get your specific information security answered by one of our experts. ChooseWhat Small Business Forums